Low-code automation for SecOpsThe SOAR platform you want. In hours, not weeks.
Mountains of monotonous tasks make building and monitoring your workflows a chore. Not anymore.
The world's most popular workflow automation platform for technical teams including
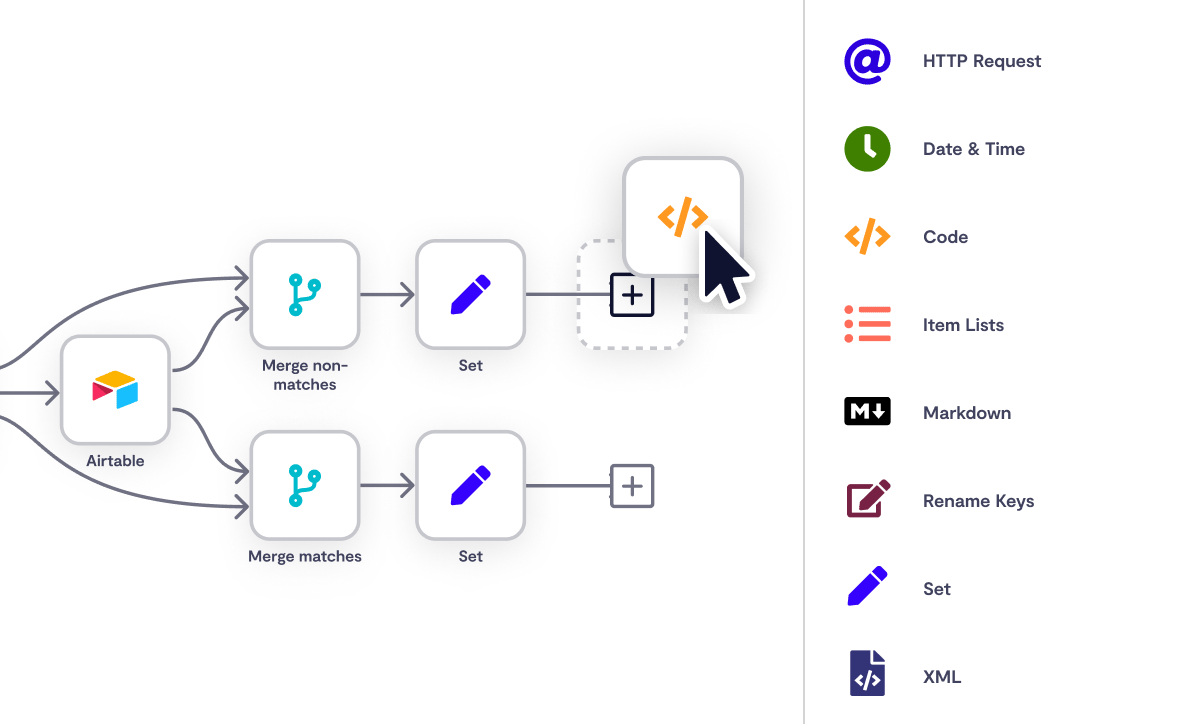
WorkflowsWorkflows that anyone can work out
Explaining mammoth Python scripts is painful when most of your team can’t code. With n8n, you can bring everyone together to build workflows with a low-code UI. And keep the power of full code with a built-in editor for when nothing else will do.
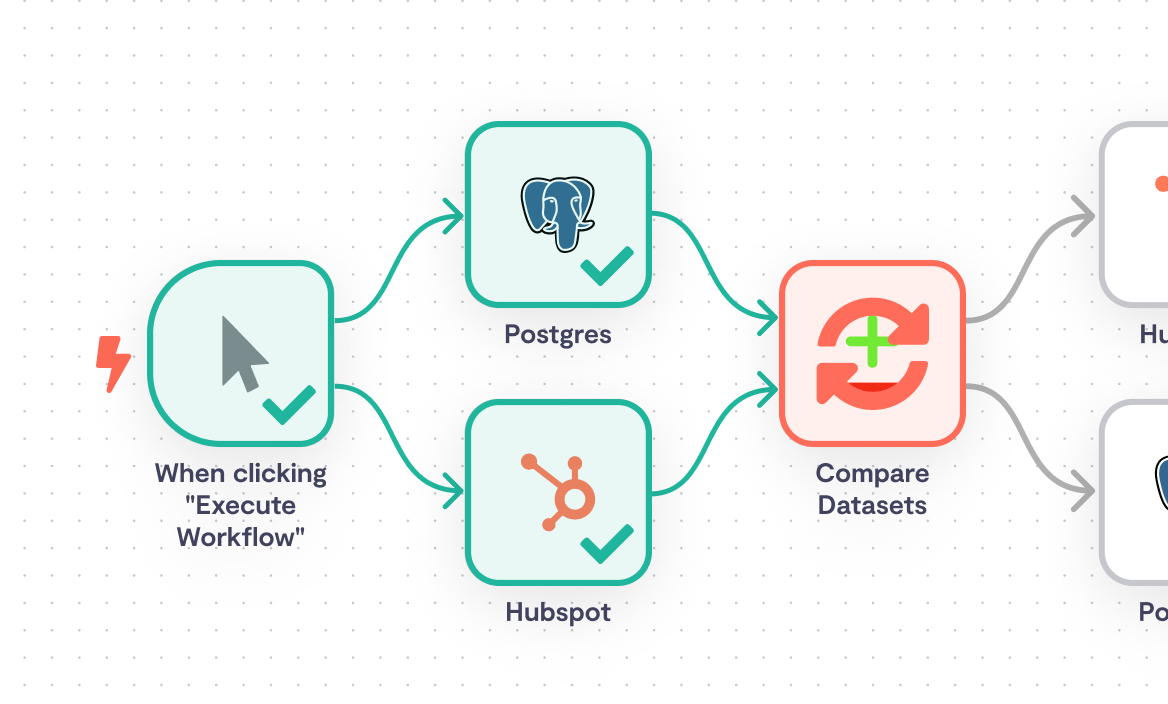
Drag n’ drop builder Connect apps without a line of code
Build workflows without worrying about APIs or authentication using our drag n’ drop visual workflow builder. Even devs get more done with the right kind of UI.
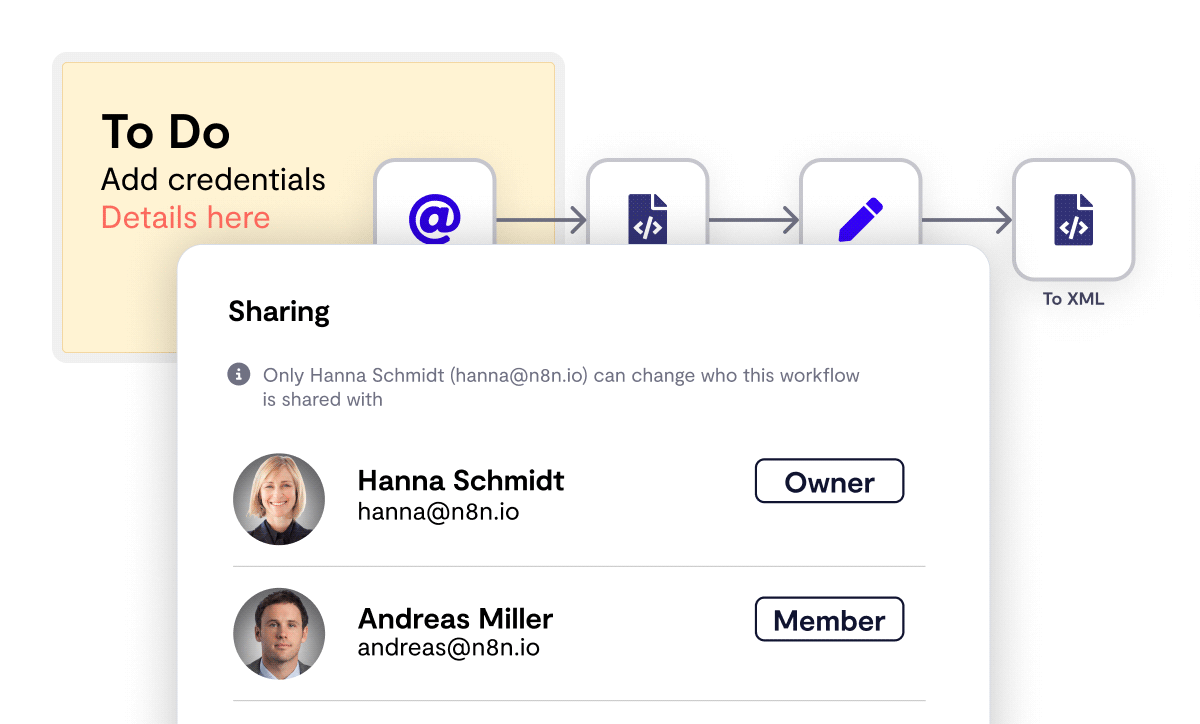
Visual interface Zero-hassle handovers
The visual representation gives anyone on your team an instant overview of what your workflow does. You can even leave sticky notes for extra clarity when required.
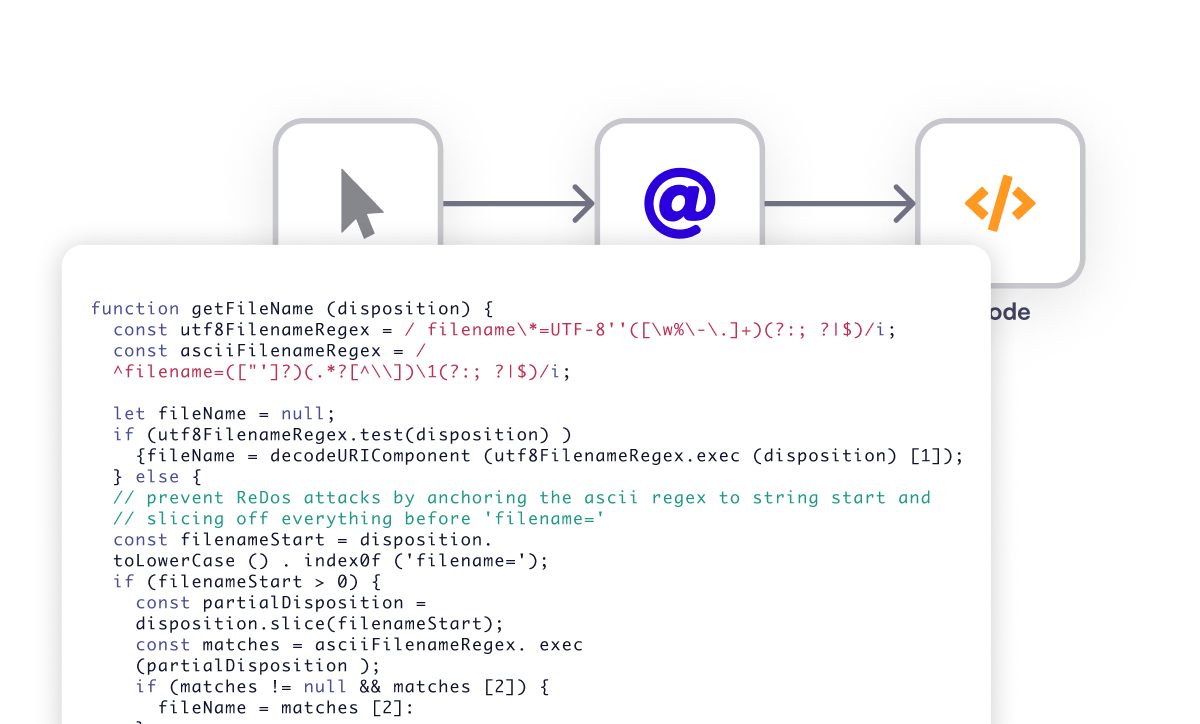
JavaScript & Python code editor Code when you need it
Write vanilla Javascript or Python with a built-in editor to insert code steps into your workflow. Because you should never feel constrained by an operation that only takes one line of code.
Template libraryYou won’t have to reinvent the workflow
Create workflows in minutes with 70+ ready-to-go ITOps templates — and counting. Our developer community adds new templates to the library for common use cases every month.
SecOps FeaturesMassive workflows. Tiny feedback loops.
You write better code faster when you can test and tweak your work in small chunks. N8n’s iterative approach lets you build workflows in the same way.
- Watch your workflows execute in real time as you build them.
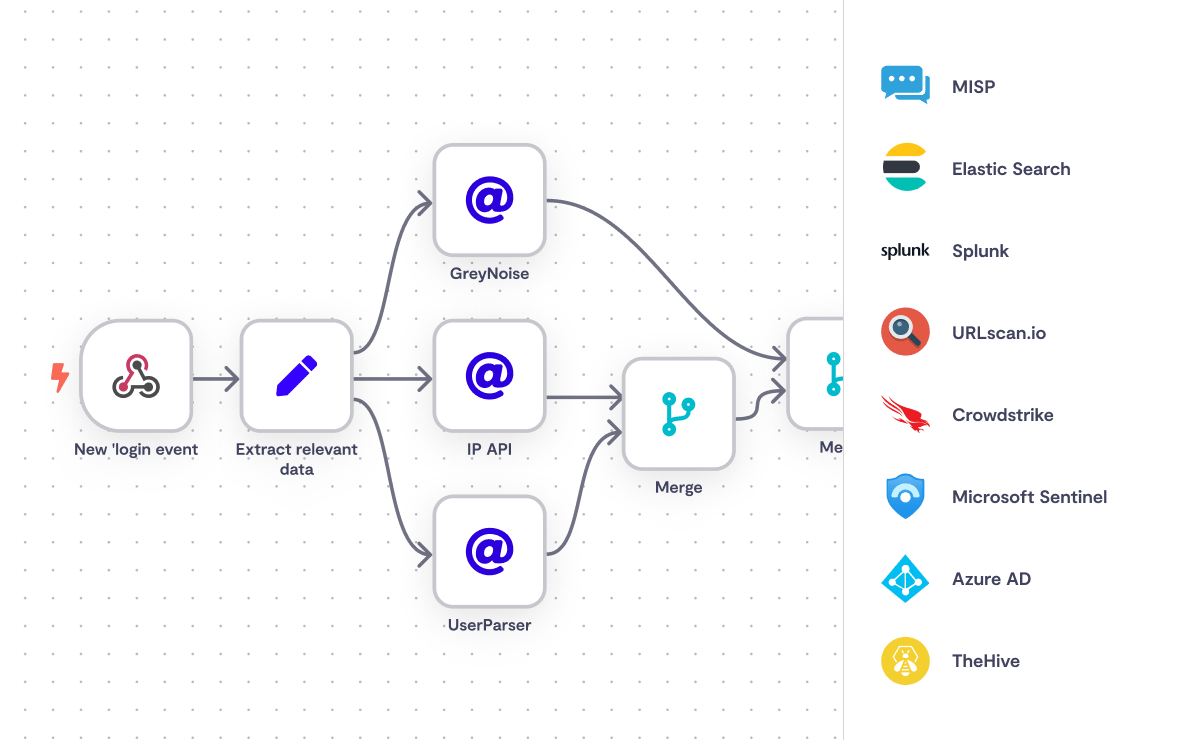
IntegrationsConnect to everything in your SecOps stack
Plug in n8n to all your go-to SIPs and TIPs with 350+ native integrations.
The value of n8nAs serious about security as you are

Encrypted credentials store
Your sensitive data is kept encrypted at all times on servers based in Frankfurt, Germany. With zero exposure to other users.

Self-hostable
Deploy fully on-prem via Docker or K8s (in <10 mins). Or run n8n air-gapped on your VPN.

Auditable source code
n8n is source code available. So you can be 100% confident about how it works by looking inside for yourselves.

German security standards
No country has a reputation for prioritizing user privacy like Germany. Our team is based in Berlin. Not a coincidence.